Imagine this: you’re sitting at your dinner table, enjoying a quiet moment with family, when suddenly your Alexa device chimes in with, “I’m sorry, I didn’t quite get that.” Or, perhaps, you’re on the phone discussing something personal, and Siri decides to say, “Here’s what I found on the web for that.” These interruptions have become so common that many of us brush them off as quirks of technology. But let’s dig deeper: are these devices simply malfunctioning, or is something—or someone—always listening?
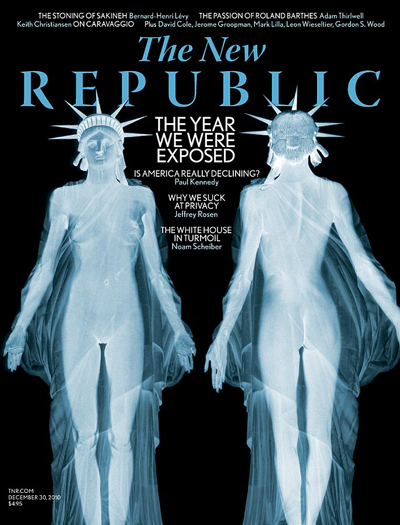
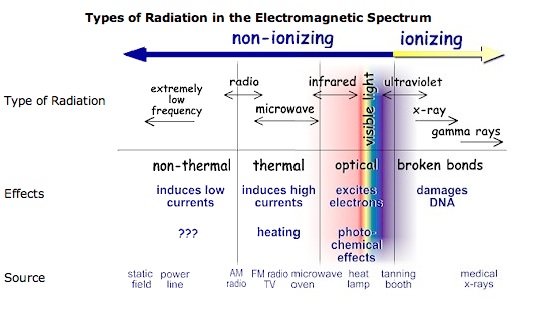
The truth is, we are constantly being watched, listened to, and monitored, whether by our smart devices, security cameras, or even the apps running silently on our phones and computers. It’s easy to dismiss this as paranoia, but let’s be real—can you honestly say you’re not being spied on?
From the blue and red squiggly lines under text that suggest grammar improvements to the ever-watchful eyes of your doorbell cameras, surveillance has seamlessly integrated into our lives. This brings up a profound, and somewhat unsettling, question: how do we reconcile with the fact that we’re always being observed? To explore this, let’s turn to some familiar “watchers” from our cultural and spiritual lore—Santa Claus, the Elf on the Shelf, and even Jesus Christ.
The Elf on the Shelf is a playful holiday tradition meant to inspire good behavior in children. The idea is simple—this magical little elf watches from its perch and reports back to Santa each night. For kids, this can be an effective way to curb naughty behavior during the Christmas season. But think about it: the elf is a symbol of constant surveillance. It’s always watching, silently judging, and subtly influencing behavior.
Sound familiar? Today’s smart devices function much like that elf—quietly perched in the background, observing your every move. The difference? Unlike the elf, these devices don’t just report back to Santa; they report back to corporations, data warehouses, and sometimes even hackers.
The idea of Santa Claus himself is a bit unnerving when you think about it. He “knows when you are sleeping, he knows when you’re awake, he knows if you’ve been bad or good…” Essentially, Santa is the original overseer of behavior. His omnipresence teaches children to act kindly and responsibly, but it also introduces them to the concept of being judged by an unseen force.
In many ways, the modern surveillance state operates on the same principle. Whether it’s the little cameras at traffic lights or the algorithms analyzing your Google searches, the message is clear: someone is always watching. And just like Santa, these systems reward or punish based on your behavior. Stay “good,” and you might get a targeted ad for something useful. Step out of line, and you could face consequences—like a flagged social media account or even legal action.
In countries like China, a social credit system is not just an idea; it’s a developing reality. The government uses vast networks of surveillance cameras, facial recognition, and AI algorithms to monitor citizens. Your online activity, financial habits, and even the company you keep can affect your score. A low score might result in:
Being banned from purchasing train or plane tickets.
Losing access to loans or financial services.
Public shaming through “blacklists” that display your name and offenses for all to see.
While this level of control hasn’t reached every corner of the globe, the infrastructure for similar systems exists in many other countries. And as digital currencies and surveillance technologies become more widespread, the potential for similar programs to emerge elsewhere becomes increasingly plausible.
For many, Jesus represents the ultimate example of omnipresence and moral accountability. The idea that Jesus sees all and knows all is a cornerstone of Christian faith. Unlike the Elf on the Shelf or Santa Claus, however, Jesus’s watchfulness is rooted in love and grace, not judgment or manipulation. His constant presence is meant to provide guidance and comfort, rather than inspire fear.
The spiritual parallel here is worth noting. While surveillance technology often feels invasive and self-serving, it’s also possible to view it as a tool for accountability and safety. For example, the cameras on your doorbell might feel like an invasion of privacy, but they also provide a sense of security. In this way, our modern surveillance landscape mirrors both the benevolent and intrusive aspects of these watchers—helping us, but also keeping us under constant scrutiny.
Living Under the Watchful Eye: Embrace It or Escape It?
Now that we’ve established that surveillance is everywhere—whether through Alexa, Nest cameras, or even the principles baked into cultural icons like Santa—it’s time to ask yourself a critical question: how do you want to live with this reality? Should you embrace the fact that you’re being watched, or is living off the grid truly a better option? Let’s examine both paths.
Option 1: Embrace the Watchfulness
If you choose to embrace the fact that you’re being watched, here’s a potential mindset shift: instead of seeing surveillance as a violation of privacy, view it as an opportunity for accountability. For example:
Use smart devices to your advantage by customizing privacy settings and understanding what data they collect.
Accept that surveillance is a trade-off for convenience. Your Alexa might “listen,” but it can also make your life easier by setting reminders, controlling smart lights, or ordering groceries.
Focus on transparency. Ask yourself, “What am I willing to share in exchange for the benefits I get?” By being mindful of what you post, type, and say near these devices, you can maintain a sense of control.
Option 2: Escape the Grid
Living off the grid is a tempting way to escape the watchful eyes of modern technology. But before you pack your bags and head for the wilderness, consider the trade-offs:
Pros: You’ll enjoy complete privacy, fewer distractions, and a sense of independence. Without constant surveillance, you’re free to live without worrying about digital footprints.
Cons: Living off the grid means giving up the conveniences of modern life, from instant communication to online banking. It also requires significant effort to maintain self-sufficiency.
If you’re leaning toward this path, start small. Try disconnecting from unnecessary tech for a weekend or limiting your use of surveillance-heavy apps. See how it feels before committing fully.
Action Plan: Finding Your Balance
Whether you choose to embrace surveillance or strive for a life of minimal exposure, here are some steps to help you navigate this hyper-connected world:
Audit Your Devices: Take stock of all the devices in your home. Adjust privacy settings, disable unnecessary features, and research what data they collect.
Be Mindful Online: Think before you post, search, or share. The less data you give away, the less you have to worry about being tracked.
Adopt Healthy Boundaries: Use technology intentionally. Set “unplugged” hours during your day to avoid unnecessary exposure to screens and microphones.
Educate Yourself: Stay informed about how surveillance works. The more you know, the more empowered you’ll feel to make choices that align with your values.
Experiment with Minimalism: Try reducing your reliance on smart gadgets. Can you live without Siri for a day? How about a week?
From Santa Claus to the Elf on the Shelf, and now the algorithms embedded in our devices, the notion of being watched has shifted from myth to an undeniable reality. Surveillance is no longer the stuff of folklore—it’s tangible, pervasive, and inescapable.
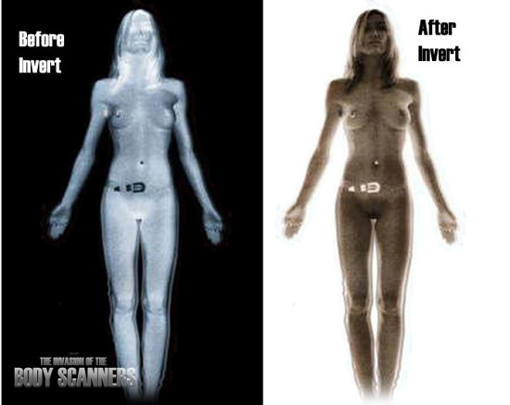
Consider programs like Israel’s Pegasus, which has the capability to remotely access cameras and microphones without users’ consent. If one nation has developed this technology, it’s safe to assume others have as well. This raises important questions: Should we allow our phones in private spaces like bedrooms and bathrooms? Should we demand devices with removable batteries to ensure they are truly “off” when we want them to be? These steps seem like prudent safeguards in a world where privacy is rapidly eroding.
In the future, we’ll dive deeper into practical tips for spotting surveillance devices in places like hotels or vacation rentals. But for now, the reality is clear—our actions and words may no longer be as private as we’d like to believe. To navigate this new era of constant observation, it’s wise to act with caution, awareness, and perhaps a touch of humor.
After all, the watchers are here to stay—whether we like it or not.
So, what will you do? Will you lean into the conveniences of modern surveillance and make peace with the trade-offs? Or will you take steps to reclaim your privacy and live life on your own terms? The choice is yours, and it’s a decision that will shape how you interact with the world in this digital age.
After all, someone is always watching. The question is: how will you respond?




































You must be logged in to post a comment.