As a matter of course, I try not to post too much about computer security, as I am certain that most have seen this before.
We know not to open attachments that are not expected as well as have good anti-virus software updated and running at all times.
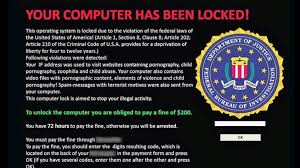
This morning I received a different type of threat that I thought worth sharing, so here it is.
With the usual jargon about some sort of violation or someone suing me for something, open the attachment to see what it is, this was different.
The words included were, “for your security we use dropbox for the evidence against you. Please follow the link and respond within 3 days or a summary judgement will be made.”
Of course, the return e-mail address is bogus; the trick is to get me to open an attachment in this case on dropbox. Once downloaded there is no telling what it would do but, most certainly nothing good.
No law enforcement or government agency would work in this way even if you were expecting something from someone in this manner; it would not come in from e-mail.
Unless you are expecting it and the e-mail address is correct only then would I make a call before opening anything as an attachment.
Ransomware is working with hospitals and even government agencies paying the perpetrators, which causes them to continue with more fervor.
Practice safe computing which includes a good disaster recovery plan.
-Best
(c) All Rights Reserved 2016
Discover more from TheTimeDok
Subscribe to get the latest posts sent to your email.
