Happy Friday!
Today I want to talk about security. With the recent events involving our President, along with major companies data base’s of credit card holders being hacked, it seemed timely.
Companies either focus on cyber-security, physical security or both or neither. I realize that this statement seems ambiguous but, the simple facts are that few companies think about hiring a Security Officer, much less installing the systems to make certain that their physical plant is secure; not to mention their Data infrastructure. A security Officer is well rounded and incorporates all facets of security into their repertoire.
Part of a Disaster Recovery plan is an audit of security measures taken.
Thanks to recent hacks by various outside entities, companies are becoming more in tune with things like passwords that change, that the user sets, as well as administrative passwords that also are forced to change and be “strong in nature.”
Instead of vilifying some of my clients practices which; many would find audacious, some entertaining, and some down right stupid; allow me to pontificate about “security in a nutshell.”
Let’s start with the employee.
All employees (present and future) should have a background check completed. Are they who they say that they are and do they have any criminal history? What is their credit score and, can they pass a “drug test” now and at some future date?
What someone writes on their resume is not a legal document therefore; you must necessarily have them fill out an application for employment which “is a legal document.” You can buy these at Office Depot, so there is really no excuse not to do this.
The resume is an instrument to get a person in the door for an interview, not to hire them by. What one writes on the application are grounds for termination, if fabricated. I can write that I am King of the Emirates on my CV, if that gets me in the door, so be it. Once I write that on an application, I have committed fraud.. Some would argue that the CV should me more sacrosanct than it is. That would be nice but the truth is, that few do.
There is a complete art regarding your CV and making it stand out among others. Like English 101, it is subjective, research the company to whom you are sending it to. That is why one must have several different resumes. I will not belabor that point or this subject here, suffice it so say, if it gets me past the first cut that is all that I care about. Until you are sitting in front of a person who gets to know you personally and uniquely from the masses, your resume is one of tens of thousands languishing in a sea of anonymity.
Once your HR department is satisfied that this person is a viable candidate for the job at hand; then and only then, should the hiring manager start the interview process.
Q. What difference does it make if the person has a less than stellar history?
A. If they have a track record for making bad decisions, there is nothing to stop them from doing so again. Once you hire them, they represent you and or your company.
Q. What difference does it make regarding their credit score?
A. If they have a lousy credit score that simply means that once again they have a higher probability of making poor decisions and even more germane, might be someone who has character issues.
One company I know of ran reports of how many coffee creamers, sugar and toilette paper their individual branches went through. They tied that data together with the branches that had “shorts.” (Shorts meaning the cash drawer did not balance, was missing money.) The interesting thing was that the branches that used more supplies, had more shorts thus; the criminal element was behind the counter.
Q. Piss Quiz? What does a little pot, or drinking, have to do with a person being a good and faithful employee?
A. Once again we are looking at character traits. If a person plays loose with the rules, they too will have a proclivity to play loose with your rules. Good behavior should be rewarded. If someone plays by the rules, they should be first up for the job.
Q. What about pre-employment test?
A. Having total empathy for those of us who suffer from test anxiety, I am more interested in a person’s history and track record. The EU is really big on all sorts of pre-employment test to get the “brightest and best” however; as a hiring manager for most of my adult life, I am here to tell you that test are not the end all be all. If HR does their part, I trust that I can weed out the rest. While a test may give you some idea of a person’s character, remember that if they are nervous or not feeling well that particular day, the results will be skewed. You may in fact be overlooking a diamond. Get to know the person.
Once a long time ago I interviewed with Microsoft. As it happened I was suffering from bronchitis, had not slept well but; I would have still gone to work as I could function so why not go on the interview. There were several parts of the process including test of different parts. Did I know the materiel? In truth I was over qualified for the job in so many ways but I thought that working for Microsoft would be a good thing so I went through with the interview. The last part of the interview some very attractive young lady brought me into an office and ask me “Why was a pothole cover round?” In the haze of DayQuil and the anxiety of the entire process, the question threw me. I chucked at her and looked at her like I was waiting for the real question like “what are the different layers of the OSI model and how are they relevant to data communications?” That question I could have handled and was expecting; not why is a pothole cover round.
After a short period of silence which seemed like an eternity I realized that she was quite serious. “I had never thought about before.” i said, “I suppose that it might have something to do with the fact that if it were any other geometric shape, it could fall in.”
That answer was met with a dis-approving look, which again threw me; as I could not think of any other reason why.
She then started asking me another question about a farmer, and a boat, and grain, and chickens, and a fox, and a river..
At this point in the process I ended the interview. I was not feeling well and this to me seemed like games that one might play with someone who had never worked in the industry before; not someone who had the years doing this that I had.
My next job was that of an IT Director (instead of working at Microsoft) , where I would be the one in charge of purchasing tens of thousands of dollars at at time of software from “Microsoft.” Microsoft has a tendency to hire a lot of young pretty girls to do their bidding, much like the drug industry does to push their pharmaceuticals to doctors. It is good to be a customer.
Physical Security
Physical security should be well thought out. I know of some companies that think this is too-expensive or don’t want to invest in this. They have a key pad entry that they change once a quarter or so, if they think about it. I have seen others who simply use a lock and key and they don’t even change them out when they have employee turnover.
Q. What should my building security look like?
A. Depending upon your business, let’s take a typical office environment.
The reception area has your normal door locks for after hours as well as video surveillance. Today we have technology that allows surveillance to be somewhat obscure but not so much so that the people who come into the lobby don’t notice it. Today’s casinos for instance have tons of cameras and you know that if you scratch yourself someone somewhere watched you do it. My point is that they are barely noticeable. They are there and you know that they are there but you quickly might forget. Your lobby should not be intimidating because your customers come through there too however; it should be obvious that you have security.
Each entrance to areas past the reception area should be hard keyed with electronic pass devices that respond to individual key cards. Piggy backing of employees traversing these doors should be discouraged however; video surveillance of these doors from both the inside and outside will allow you to track employee movement should the need arise.
Electronic time clocks which use RFID or even bio metrics are not only good for payroll but, once again a good way to track employee movement. Again the clock(s) should have video cameras in them and pointed at them so there is no way someone could be clocking in someone other than themselves. The more secure the area is, the more visible you should make your security.
Depending upon your organization doors, controlling access to certain areas aka HR, development, data center etc should be keyed to allow only people with a need for entrance to that area. Again these doors are also under video surveillance from both the inside and outside.
Employee cards should have a picture of the employee on them and should be visible at all times when the employee is on campus.
With unique employee key cards and programmed entrance to the areas that each unique employee will need, the only changes to the system will be when that employee leaves and it only has to change with that one person.
Not only does this give your physical building / plant a security that this day and time calls for but, it allows you to track your employees movements if the need arises.
Q. Why would I need to track an employee?
A. Lets say you have an area of production that is suffering and you don’t know why. What if you pulled a report and found that your manager of that area was spending a lot of time in places other than where he or she should be? This actually happened at one of my clients. They had several thefts one night and found that by tracking the people that came and went and correlating those times with security footage were able to actually see the person perpetrating the crime. This person spent some time behind bars and the company was quickly able to remove undesirable elements from their work staff.
Q: Is there any other physical security measures that I should look at?
A: Glass breakage detectors, motion detectors, smoke and gas detectors and I like to add water detection equipment. The later inclusion would have come in handy a couple of times in my career. We were in the middle of a remodel and one of the plumbers forgot to solder a fitting. They turned on the water and it held pressure so they left. Sometime over the weekend the fitting let loose and the entire building was flooded. Water detection sensors would have kept the damage to a minimum instead of flooding an entire high rise. Since most fire suppression system are water, this too would let you know if something failed with that system.
Note: there are several different fire suppression system and water is good for general purpose however; a data center needs a little more thought.
How about your computer systems? While the above is an abbreviated look at employee and physical security, what about your data?
- Passwords that change
- Cable infrastructure
- Admin passwords that change and are strong
- Firewalls with the appropriate updates and configurations
- SNMP manageable devices that are updated and set to user specific user name and passwords
- Physical cable plant that is locked down to only allow access from expected devices.
- WiFi that is locked down
- VLANS segregating departments and traffic
- Servers with specific access to files and or data needed by departments and or users.
- S.A.M. (Software Asset Management) in place and kept up to date
- VPN encrypted access with security token
- All outside connections to the network identified and locked down.
- Roaming profiles up dated and checked for security
- No remote control software on company computers either remote or host.
- Admin access to user computer restricted or not at all.
- Thumb drives and laptops encrypted.
You would be shocked if I told you how many times I find loose if not non-existent password policies. It is almost as if they are begging for industrial espionage or begging some disgruntled employee to have their way with them.
Much like having a PC without a locking screensaver is down right idiocy; these folks beg to be burned.
User passwords must change every 90 days at max and should be strong, meaning special characters, numbers and so forth. One company that I know of keeps a spreadsheet of everyone’s assigned password that never changes. That keeps the sys-admin from re-setting passwords but opens the company up to so many security violations it is unbelievable. This practice is in direct violation of policies set forth for publicly traded companies, and those that follow ISO standards.
Admin or super user passwords should also change on no particular date but often, more often than every 90 days but with no predictability. There might be some inventive programmer who could write an app that would randomly go off and invoke a password change for administrators and not let you continue on until you have done so.
Another ambiguity with our illustrious data folk is a lack of documentation with their data plant. Why is that important?
In the server room that contains the switches should be a map. This map should contain a map of each floor and the data drops. Not only should these drops be labeled as such they should be secured. How do you secure a data drop and why?
Let’s start with the Why? If I were a bad guy I might come in disguised as a janitor. I would have a small laptop and that would have on it some software to sleuth your network with my goal being to get into your servers. The first thing that I would do is find a data port that had nothing in it and plug right in “assuming that there was no wifi that I could get into.”
Now if you do your cable management correctly, that vacant port that I just plugged into is not hooked up via the patch panel. That forces me to go unplug a computer or printer and try it there as that is an active device so it is cabled.. In our switch we can have it only talk to the device if it is the MAC address that it is programmed to expect. The idea is to make it is difficult as possible for the would-be intruder to gain access to your data.
In most shops, we have no idea what drops are live, and where they are or what they are, much less what is plugged into them.
With VLAN’s we offer yet another layer of security in that if this guy plugs into some port that the secretary uses, he will not be able to get access to the engineers VLAN.
Many times I see networks where more ports were needed so a switch was just thrown into the drop, problem solved. This is poor on many levels. Anyone with any networking sense knows better but yet I see it every day. You take a multi-thousand dollar cable plant and install a $30 switch screwing up collision rates, security, traffic throughput and so forth rather than do it right.
Jumping down the list to S.A.M. While most things on this list are common sense S.A.M. might not be that intuitive.
Q. Why do I need to keep up with what is on each and every computer and how does that relate to security?
A. Really good question. In running an audit of all software on all computers within an organization you will quickly find that your organization has a lot of software that the business owner is responsible for. If some disgruntled employee calls the Business Software Alliance http://www.bsa.org/ and reports that you are using pirated software; it then becomes your responsibility to prove otherwise.
- Can you show proof of purchase for all software within your organization?
- Can you show the license keys for that software, if so, prove it to yourself.
- Do you know what each and every executable is on each and every desktop?
- Do you have software on computers that is not being used?
The long and the short of this exercise is that I do an inventory of software on PC’s as part of a DR. While this is a painful exhaustive process, it is important because you have to know what you have, if you want to re-create it in the case of a disaster.
I always find software that the company was unaware of.
I most always find Trojans, viruses, games and more importantly, I find remote control software.
While this is a real good reason why people should not have access to the administrative rights on their computers, it is also a real good reason to do this inventory.
The normal computer user does not need to modify their computer to use word, excel and power point. IT should be in charge of adding software and then the PC should stay fairly static.
Remote control software is used to either allow a user to take control of their computer from outside the building or control another PC outside the building or inside the building. Maybe that is perfectly legitimate or very possibly it is not. That Is why I insist that things like copy inhibit, and auditing, be enabled on the servers. If forensic investigations are needed down the road, we have the tools to do so, we simply must use them.
Industrial espionage is real and the business owner should take it real seriously. There are “certifications for data security experts” out there. What I know of this stems from over 30 years of doing this. It actually might be interesting to go through the class and see what I have not thought of.
A word about industrial espionage.
People often wonder if I struggle with paranoia. I assure you that I am purrrfectly normal, I don’t struggle, I submit to it; everyone has their children followed, and thinks that their cats are spying on them, right?
So I am not a comedian..
The idea that I wanted to mention here is really from WWII. “Loose lips sink ships.” The idiom means “beware of unguarded talk.” No, I am not that old but; I am a student of history among other things. We live in a high-tech world and we live in a social world. We have several areas of town where there are high tech industries and where employees of those industries gather for lunch, or to have a beer and shoot pool after work. Too many times I am in ear shot of engineers talking shop, in public. If you own or manage a company that has “secrets” I would caution your employees about talking shop in public. There are most likely posters that someone sells that you could hang on the wall as a subtle reminder about this subject.

The above picture proves that this concept is not lost on today’s companies.
If I worked at company Y who had company X as a competitor, I might very well have someone go down to the area where company X was and scope out restaurants where there were known hangouts for their engineers or technical guys. I might also; if I were unscrupulous, have someone go stake out the place and make certain that I had them there when their folks had lunch. In this day and age where there is a complete science behind “blending in,” it would be rather easy to go eaves drop. In this day of technology, bugging someone would not be out of the realm of possibility. When fountain pens that are a self-contained Digital Video Camera / Recorder which can record up to an hour per charge are less than $20; you had best beware that your cats may very well be spying on you. Ok, not your cats, but certainly your employees or strangers.
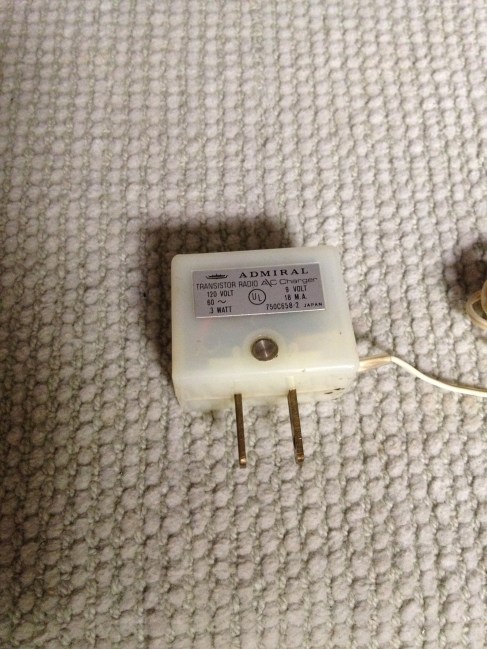
Thinking back to Mission Impossible, where the tape recorder would start spewing smoke out ten seconds after the message had been listened to, devices are worth mentioning here.
Devices that leave the confines of the building; in this case laptops and thumb drives need to be secure. Folks it is downright foolish not to have these things encrypted. We have so many different types of encryption techniques available today. Encrypting your data should it fall into the wrong hands will still make it useless to those who take it. Even the smart phone has a failsafe built into it.
Because we store so many things on our Smartphone’s, they are more than just a phone. The courts recently rules that police can no longer take your phone and access it to see what you have been up to as the phone is so much more than a simple phone. My iPhone for example after X attempts to guess my password will wipe itself. Can we write such security programs for thumb drives and laptops? Not a programmer; well since COBOL, but I am guessing that it is do-able.
Is the Cloud safe?
At this point in time, I would say no. As much as we hear how safe that it is, each and every day we also hear about how it was violated, or how some major organization was hacked.
Back up your data and send a copy to your safe deposit box at the bank. Make certain that your safe deposit box is a few miles from your office or residence so that if a tornado or other type disaster takes out your business or residence, your data stored in that safe deposit box and is still there. Utilize a service to take your data off site if you like, or set up your own “cloud” via a secure tunnel over the internet to another location.
Hard drives are cheap and UNIX or Linux is not all that difficult to use to set up an FTP server. While anything is better than nothing, have a strategy and test it; even if you do use the cloud.
With the White House being violated by a crazy person, the president in an elevator with a known criminal with a gun, not to mention the secret service allowing him to go to Mandela’s Funeral and speak just a few feet away from the translator who was not who he said he was, we must question everything.
The only way to really trust that your data is safe and for that matter your business or residence; is to test your plan once you implement it. There are people you can hire “good guys” that will test your security from different angles as well as your disaster recovery plan.
The framework above is an excellent starting point. Trust me when I say this, many CEO’s have no idea how vulnerable they are as they trust that their CIO or SysAdmins know this stuff. Each and every DR that I do, I find that most do not. The more that I dig; the more truculent these folks become and are really happy when I leave. They don’t want their boss’s to know the truth. While I would happily work with them to fix these things and offer as much, they would rather hide the facts from those that should know their vulnerabilities.
If you are a CIO or head of a company that is interested in this, read my blog “attention CIO CEO ….
-Best to you and those that you care about!
Good Luck Jim
Copyright 2014 All rights reserved
The below is an addendum to this article which really puts things into perspective…
FOR IMMEDIATE RELEASE
Tuesday, September 30, 2014
Four Members of International Computer Hacking Ring Indicted for Stealing Gaming Technology, Apache Helicopter Training Software
Four members of an international computer hacking ring have been charged with breaking into computer networks of prominent technology companies and the U.S. Army and stealing more than $100 million in intellectual property and other proprietary data. Two of the charged members have already pleaded guilty. The alleged cyber theft included software and data related to the Xbox One gaming console and Xbox Live online gaming system; popular games such as “Call of Duty: Modern Warfare 3” and “Gears of War 3”; and proprietary software used to train military helicopter pilots.
Assistant Attorney General Leslie R. Caldwell of the Justice Department’s Criminal Division, U.S. Attorney Charles M. Oberly III of the District of Delaware and Special Agent in Charge Stephen E. Vogt of the FBI’s Baltimore Field Office made the announcement.
“As the indictment charges, the members of this international hacking ring stole trade secret data used in high-tech American products, ranging from software that trains U.S. soldiers to fly Apache helicopters to Xbox games that entertain millions around the world,” said Assistant Attorney General Caldwell. “The American economy is driven by innovation. But American innovation is only valuable when it can be protected. Today’s guilty pleas show that we will protect America’s intellectual property from hackers, whether they hack from here or from abroad.”
“Electronic breaking and entering of computer networks and the digital looting of identities and intellectual property have become much too common,” said U.S. Attorney Oberly. “These are not harmless crimes, and those who commit them should not believe they are safely beyond our reach.”
Nathan Leroux, 20, of Bowie, Maryland; Sanadodeh Nesheiwat, 28, of Washington, New Jersey; David Pokora, 22, of Mississauga, Ontario, Canada; and Austin Alcala, 18, of McCordsville, Indiana, were charged in an 18-count superseding indictment returned by a federal grand jury in the District of Delaware on April 23, 2014, and unsealed earlier today. The charges in the indictment include conspiracies to commit computer fraud, copyright infringement, wire fraud, mail fraud, identity theft and theft of trade secrets. The defendants are also charged with individual counts of aggravated identity theft, unauthorized computer access, copyright infringement and wire fraud.
Today, Pokora and Nesheiwat pleaded guilty to conspiracy to commit computer fraud and copyright infringement and are scheduled for sentencing on Jan. 13, 2015. Pokora was arrested on March 28, 2014, while attempting to enter the United States at the Lewiston, New York, Port of Entry. Pokora’s plea is believed to be the first conviction of a foreign-based individual for hacking into U.S. businesses to steal trade secret information.
According to the superseding indictment and other court records, from January 2011 to March 2014, the four men and others located in the United States and abroad allegedly hacked into the computer networks of Microsoft Corporation, Epic Games Inc., Valve Corporation, Zombie Studios and the U.S. Army. The defendants and others allegedly obtained access to the victims’ computer networks through methods including SQL injection and the use of stolen usernames and passwords of company employees and their software development partners. Once inside the victims’ computer networks, the conspirators accessed and stole unreleased software, software source code, trade secrets, copyrighted and pre-release works and other confidential and proprietary information. Members of the conspiracy also allegedly stole financial and other sensitive information relating to the companies – but not their customers – and certain employees of such companies.
Specifically, the data cyber-theft allegedly included source code, technical specifications and related information for Microsoft’s then-unreleased Xbox One gaming console; intellectual property and proprietary data related to Xbox Live, Microsoft’s online multi-player gaming and media-delivery system; Apache helicopter simulator software developed by Zombie Studios for the U.S. Army; a pre-release version of Epic’s video game, “Gears of War 3;” and a pre-release version of Activision’s video game, “Call of Duty: Modern Warfare 3.” The defendants also allegedly conspired to use, share and sell the stolen information.
The value of the intellectual property and other data that the defendants stole, as well as the costs associated with the victims’ responses to the conduct, is estimated to range between $100 million and $200 million. To date, the United States has seized over $620,000 in cash and other proceeds related to the charged conduct.
In addition to those charged in the United States, an Australian citizen has been charged under Australian law for his alleged role in the conspiracy.
An indictment is merely an allegation, and the defendants are presumed innocent unless and until proven guilty in a court of law.
This case is being investigated by the FBI, with assistance from the Criminal Division’s Office of International Affairs, the U.S. Department of Homeland Security’s Homeland Security Investigations and Customs and Border Patrol, and the U.S. Postal Inspection Service. The investigation also has been coordinated with the Western Australia Police and the Peel Regional Police of Ontario, Canada.
The case is being prosecuted by Trial Attorney James Silver of the Criminal Division’s Computer Crime and Intellectual Property Section and Assistant U.S. Attorney Edward J. McAndrew of the District of Delaware.























You must be logged in to post a comment.